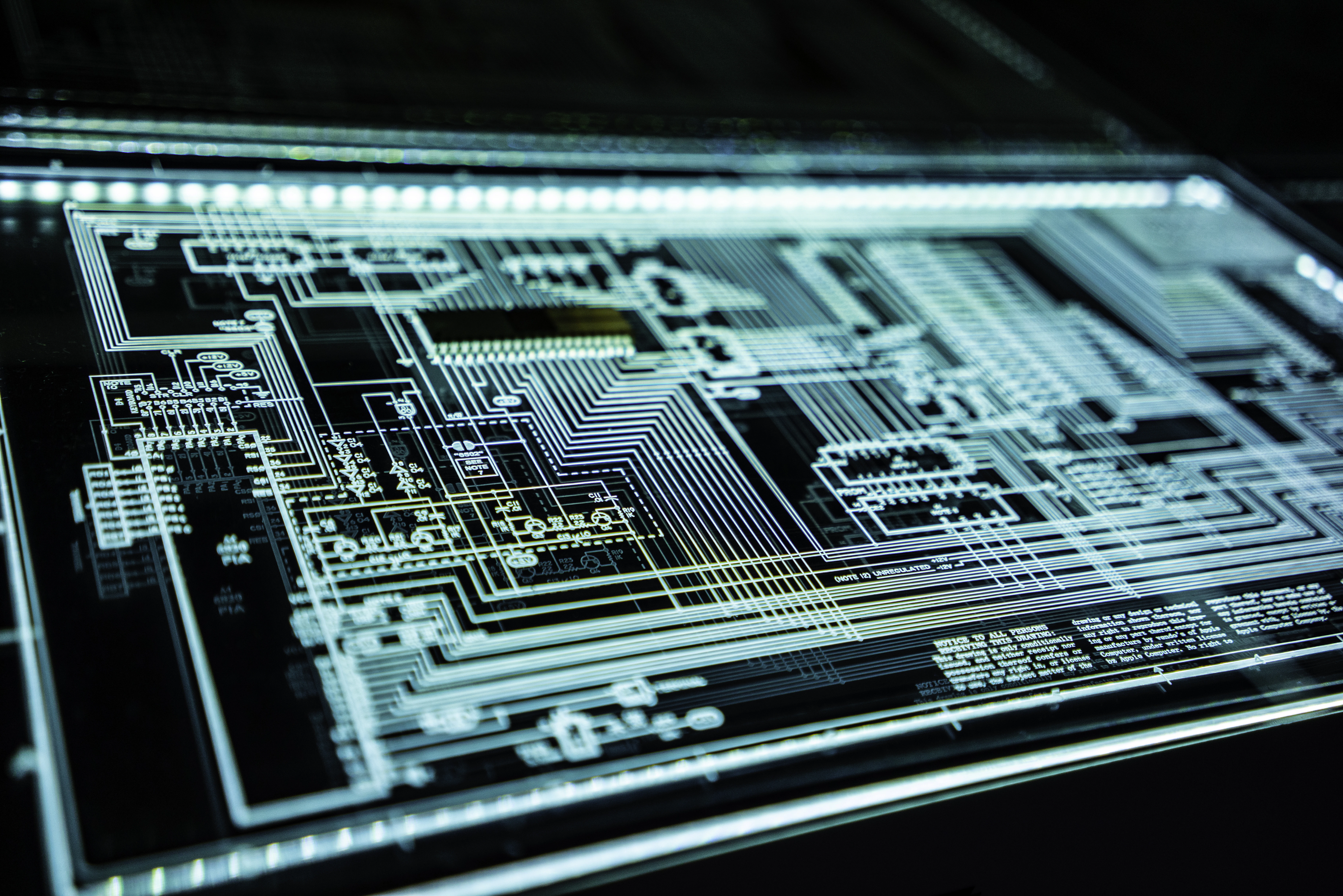
ARCHIVED OPERATIONS
RECOLLECTIONS
Relive the most significant cyber events in history. Step into the shoes of the attackers, defenders, and analysts. Understand the strategy, the code, and the impact of legendary exploits.
Global Impact
Real-world scenarios
Multi-Perspective
Red, Blue, & Purple Team
More Archives Declassified Soon
Our intelligence team is constantly declassifying new operations.